GFW Technical Review 14 – The Cat and Mouse Game

Over the course of this series, we have traced two decades of evolution of the Great Firewall and the tools built to circumvent it. Each generation of tool was a response to the GFW’s latest adaptation, and each adaptation forced the next innovation from the circumvention community.
In this final post, we take a step back and examine the structural dynamics of this arms race: the asymmetries that shape it, the strategic trade-offs that constrain both sides, and the broader trends that will determine where it goes next.
The Asymmetries
The arms race between the GFW and the circumvention community is not a contest between equals. Both sides operate under fundamentally different constraints, which is why the race plays out the way it does.
Resources
The GFW is backed by the resources of a state. It has dedicated funding, full-time engineering teams, access to specialized hardware, and the authority to command state-owned ISPs to deploy infrastructure at the network backbone. It can purchase enterprise DPI equipment, commission custom silicon, and operate at a scale that no volunteer community can match.
The circumvention community, by contrast, is a loose, largely volunteer-driven ecosystem. Most major tools (Shadowsocks, V2Ray, Xray, Trojan, Hysteria) were created by individuals or small teams working in their spare time. Funding is scarce and coordination is informal.
Agility
Despite the resource disadvantage, the community has an edge in speed. A single developer can publish a new protocol or patch a vulnerability far faster than new technologies and policies can filter through a bureaucracy. When the GFW makes a change, the community can often respond within weeks. Countering a new circumvention protocol, by contrast, requires the bureaucratic machine to go through early research, funding applications, R&D, testing, experimental deployment, and finally large-scale rollout, a process that can take years.
Openness
The circumvention community operates almost entirely in the open. Source code is published on GitHub. Protocol specifications are documented in public repositories. Academic papers analyze both the GFW’s techniques and the circumvention tools’ weaknesses. This openness is a strength, enabling peer review, rapid iteration, and broad adoption. But it is also a vulnerability. The GFW’s engineers can read the same source code, study the same specifications, and use the same research to develop countermeasures.
The GFW, conversely, operates in near-total opacity. Its filtering rules, detection algorithms, and infrastructure architecture are not publicly documented. What the community knows about the GFW’s capabilities comes from empirical testing, traffic analysis, and occasional leaked documents. This information asymmetry means the circumvention community is always, to some degree, fighting blind, building defenses against capabilities it can only infer.
Data
The GFW has access to something the circumvention community fundamentally lacks: the data. Sitting at every international gateway, the GFW observes all cross-border traffic. This position enables machine-learning-based classification: train a model on labeled traffic data and extract statistical features across millions of connections. The volume and diversity of the training data available to the GFW is immense, and it improves with every connection that crosses the border. The GFW could even be intentionally allowing some traffic through just to collect more data.
The circumvention community has no comparable dataset. Developers can test their tools against the GFW empirically (send traffic and see what gets blocked), but they cannot observe the GFW’s decision-making process or access its training data. They are, in effect, trying to evade a classifier they cannot inspect, trained on data they cannot see.
Cost
There is, however, one asymmetry that heavily favors the circumvention community: the cost of making mistakes. When the GFW blocks a connection, it risks collateral damage: disrupting legitimate traffic, breaking business services, degrading the internet experience for ordinary users. When a circumvention tool fails, the cost is borne by individual users who temporarily lose access. The GFW must be conservative because its errors are visible and politically costly; the circumvention community can be experimental because its failures are private and recoverable.
The Strategic Landscape
The Classification Problem
The GFW’s fundamental challenge is a binary classification problem: given a stream of network traffic, determine whether it is a proxy connection or legitimate traffic, and do so in real time at national scale.
In the early days, this was simple classification with clear decision boundaries: keyword-based pattern matching and URL-based blocking. With the introduction of fully encrypted and TLS-based evasion protocols, those clear boundaries collapsed. The GFW responded by moving to multi-dimensional, probabilistic models that combine multiple feature dimensions.
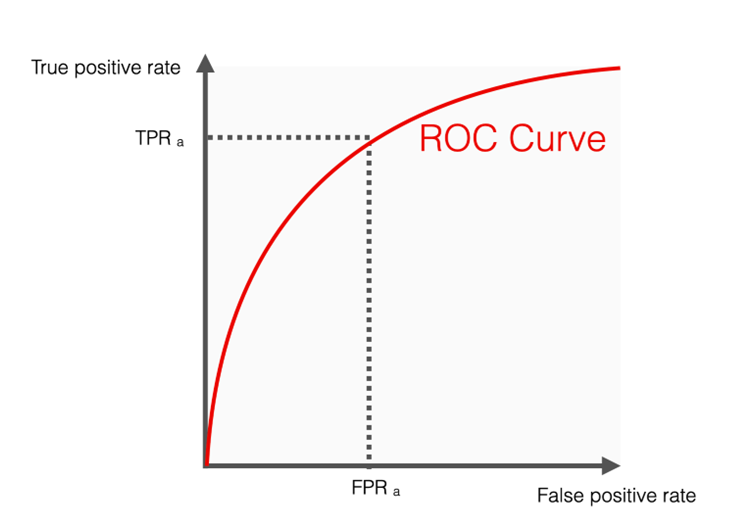
This puts the censor in a classic binary classification dilemma: the trade-off between precision and recall. To improve recall (catching as much circumvention traffic as possible), the classifier must become more aggressive. But aggression comes at the cost of precision: an aggressive classifier inevitably inflicts a higher false-positive rate. This is a cost the GFW cannot easily bear. Even a 0.1% false-positive rate would cause major network disruption at national scale. The GFW’s classifier must therefore remain extremely conservative, at the cost of recall.
The circumvention community’s strategy is clear: make this classification problem harder. Circumvention protocols do not need to be perfectly undetectable; they only need to make detection expensive enough that the GFW’s tolerance for collateral damage becomes the binding constraint.
This dynamic shifts during politically sensitive periods. During the “Two Sessions” each year, when China’s national legislature convenes, the censor becomes noticeably more tolerant of false positives and tunes the GFW more aggressively. The classification threshold moves, and tools that work reliably in normal times may suddenly be blocked.
Look Like Nothing vs. Look Like Something
The series has traced a clear philosophical arc in circumvention design. The early protocols (Shadowsocks, VMess) took the “look like nothing” approach: encrypt everything and hope the resulting random-looking bytes evade classification. This worked until the GFW learned that “looking like nothing” is itself a signal. The TLS-based family (Trojan, VLESS, REALITY) took the opposite approach: “look like something,” specifically the most common and most valuable protocol on the internet. This strategy is more robust because it raises the collateral damage cost, but it requires getting the imitation right across every observable dimension, which is difficult.
Neither approach is strictly superior. The “look like nothing” strategy is simpler to implement and does not depend on mimicking a moving target, but it is vulnerable to entropy-based classifiers. The “look like something” strategy is harder to block but requires constant maintenance as the imitated protocol evolves: every Chrome update, every TLS specification change, every shift in typical traffic patterns demands that the circumvention tool adapt in lockstep.
The Value of Diversity
An observer might ask: why does the circumvention community keep designing new protocols? Why not standardize on one proven tool and refine it indefinitely?
The answer is that the arms race makes standardization dangerous. If the entire community converges on a single tool, as it largely has on Xray + VLESS + REALITY, then a single breakthrough in detection renders the majority of users vulnerable simultaneously. The GFW only needs to fingerprint one stack. Diversity of protocols is a form of herd immunity: each distinct tool forces the GFW to develop a separate detection capability, spreading its resources thinner.
This is also why the proliferation of tools, which can seem wasteful or confusing to newcomers, is actually a structural advantage. Shadowsocks, V2Ray, Xray, Trojan, NaïveProxy, Hysteria, sing-box: each embodies a different set of design choices and presents a different fingerprinting surface. The GFW cannot block all of them with a single rule.
The Unsolved Frontier
As we have discussed throughout this series, the fingerprinting surface has steadily migrated upward: from protocol-level signals, through TLS-level fingerprints, to infrastructure and behavioral signals that no protocol can fully address.
IP reputation is the most stubborn of these. A VPS IP on a cloud provider that hosts no popular services, receiving persistent connections from Chinese residential IPs, is inherently suspicious regardless of what protocol those connections carry. The GFW can maintain databases of IP ranges by hosting provider, cross-reference connection patterns, and assign risk scores that have nothing to do with the traffic’s content.
Connection behavior is similarly intractable at the protocol level. A user who maintains a single long-lived connection to one foreign IP for hours, with traffic patterns that correlate with web browsing rather than direct access, looks different from a user browsing the open web, no matter how perfect the TLS handshake is.
These signals are weaker and noisier than protocol-level fingerprints, but they are also harder to eliminate. They represent the next frontier of the arms race: not “can the censor identify the protocol?” but “can the censor infer the purpose of the connection from its metadata and context?”
Law Enforcement
It is illegal to use and operate censorship circumvention tools in China. While enforcing this against individual users who run their own proxy servers abroad is difficult, most people lack the technical background to do so and rely on established proxy operators instead. Much of the law enforcement effort centers on identifying and shutting down these operators. It is its own cat and mouse game: well-known operators tend to draw attention from the authorities. For the state, investing in making proxy services harder to access and riskier to operate can be more cost-effective than improving the GFW itself.
The Trends
The Academy
Censorship measurement and circumvention have attracted growing attention from the academic research community. Cybersecurity research labs at major universities, along with organizations like the Great Firewall Report, actively conduct research and analysis on the GFW’s capabilities and behaviors. Conferences like FOCI (Free and Open Communications on the Internet) focus exclusively on internet censorship and privacy, and the topic has gained growing visibility at top-tier security venues like USENIX Security. Most academic work focuses on measurement and analysis rather than building circumvention tools directly, but the growing body of research brings significant benefits to the community through deeper understanding of the GFW.
The Move Toward Encryption
The long-term trend of the internet is unmistakably toward more encryption. HTTP gave way to HTTPS. TLS 1.0 and 1.1 gave way to TLS 1.2, then TLS 1.3, each version encrypting more of the handshake and reducing the metadata visible to middleboxes. Encrypted Client Hello (ECH) aims to encrypt the SNI field, one of the GFW’s last reliable inspection points in the TLS handshake. DNS-over-HTTPS and DNS-over-TLS encrypt DNS queries that were previously plaintext.
Each of these transitions narrows the GFW’s visibility. The circumvention community did not drive these changes (they were driven by the broader internet’s demand for privacy and security), but it benefits from them enormously. The more the baseline internet encrypts, the less the GFW can see, and the easier it becomes for proxy traffic to hide in the crowd.
Internet Centralization
The internet has consolidated around a small number of infrastructure providers (Cloudflare, AWS, Google Cloud, Azure, Akamai) that serve as the backbone for much of the web. This centralization favors the circumvention community.
It raises the cost of collateral damage. When circumvention tools route traffic through Cloudflare or AWS, blocking the proxy means blocking the infrastructure provider, and blocking Cloudflare means breaking access to a significant fraction of the internet. CDN-based strategies (WebSocket through Cloudflare, gRPC through Cloudflare) exploit this directly. The providers themselves have little incentive to cooperate with Chinese censorship. But this could change if providers come under sufficient political or economic pressure to identify and drop proxy traffic from their networks.
GFW Decentralization
On the other hand, the GFW itself is becoming increasingly decentralized. The old model of censorship centered exclusively around international gateways is obsolete. Growing evidence shows GFW infrastructure being deployed throughout the national backbone network at provincial and even city level. This provides more flexibility in policy enforcement and allows different technologies to be deployed for different purposes. It also signals an organizational shift: internet censorship is no longer solely the responsibility of a national body but is increasingly shared with provincial and local governments.
The Export of the Model
The GFW is no longer unique. Russia, Iran, Myanmar, and others have built or are building similar censorship systems; recent leaks even point to direct technology exports from China to various countries. The protocols and techniques documented in this series were developed against the GFW, but they are now deployed against censorship regimes worldwide. This internationalization cuts both ways: it expands the user base and the pool of developers contributing to circumvention tools, but it also means multiple state actors are independently investing in detection capabilities, and a technique discovered by one censor can be adopted by others.
The People
Behind every tool, protocol, and technique in this series, there is a person.
Shadowsocks was created by a developer known as clowwindy, who open-sourced the project and maintained it for years – until being pressured by the authorities in 2015 and forced to cease development. Trojan, Hysteria, NaïveProxy, XTLS: each was built by individuals or tiny teams, working pseudonymously, often at personal risk, with no funding and no institutional backing.
These developers did not build circumvention tools for profit or recognition. They built them because they believed that access to information is worth defending, and because they had the technical skill and the passion to do something about it. The code they wrote is used daily by millions of people: people who read foreign news, access academic resources, communicate with family abroad, or simply use the internet the way most of the world takes for granted. It is the open-source spirit at its finest.
The arms race documented in this series is often framed as a contest between technologies. It is, but it is also a contest between the resources of a state apparatus and the determination of individuals who refuse to accept the boundaries it imposes. The GFW has the advantage of scale, funding, and authority. The circumvention community has the advantage of openness, adaptability, and something harder to quantify – the conviction that the work matters.
The cat and mouse game will continue. But as long as there are people willing to write the code, the door stays open.
References
- Evidentlyai. How to explain the ROC curve and ROC AUC score? https://www.evidentlyai.com/classification-metrics/explain-roc-curve
- Anonymous, Anonymous. Sharing our thoughts on the cat-and-mouse game. https://gfw.report/blog/thoughs_on_cat_and_mouse_game/en/
Enjoy Reading This Article?
Here are some more articles you might like to read next: